More notes on sovereignty
Consider this post to be the afterbirth of the last one. It’s the bits and pieces I couldn’t cram into the last one, which was already haemorrhaging asides, segues and diversions. As such I’ll not even try hard to connect the dots presented this time.
I thought I was done with the sovereignty posting. There are other things I want to get onto. Other half-baked rants, sketchy musings and dubious epiphanies languish in draft mode. But I blog far slower than the world moves. I still had notes I couldn’t cram into the last post. Still a few tabs open I couldn’t bring myself to exile into the cold, forgotten but persistent realm of my browser history without processing them somewhere. This is somewhere.
This one’s about another kind of digital sovereignty. The personal kind. No, this isn’t about the weird far-right movement that spawned the Nick Offerman movie. Though there are lessons in that which may cross-pollinate here. There’s this notion that people have developed: Jurisdiction curation.
Companies are noticing. It’s becoming marketing hype lexicon. LinkedIn is filthy with tech ads suddenly promising everyone their own private sovereignty in the cloud.

Some FOSS developers are getting in on it.
But everything in a cloud is just on someone else’s machine, and machines are owned by people who are subject to laws. Consider Proton. Proton sells Switzerland as part of its privacy promise. Neutrality. Mountains. Banking secrecy. Nazi gold. A jurisdiction imagined as immune from foreign power. People fill in the gaps themselves. Reality fills in the gaps as well. Guess which one wins.
Switzerland participates in the same legal mesh as everyone else. Mutual Legal Assistance Treaties (loads of these). Cross-border warrants. Structured cooperation between prosecutors who don’t care about marketing copy. Five years ago, Proton logged and handed over an IP address tied to a French climate activist after a Swiss order. More recently, payment data tied to an anonymous account was sufficient to unmask a protester in the U.S. for the FBI.
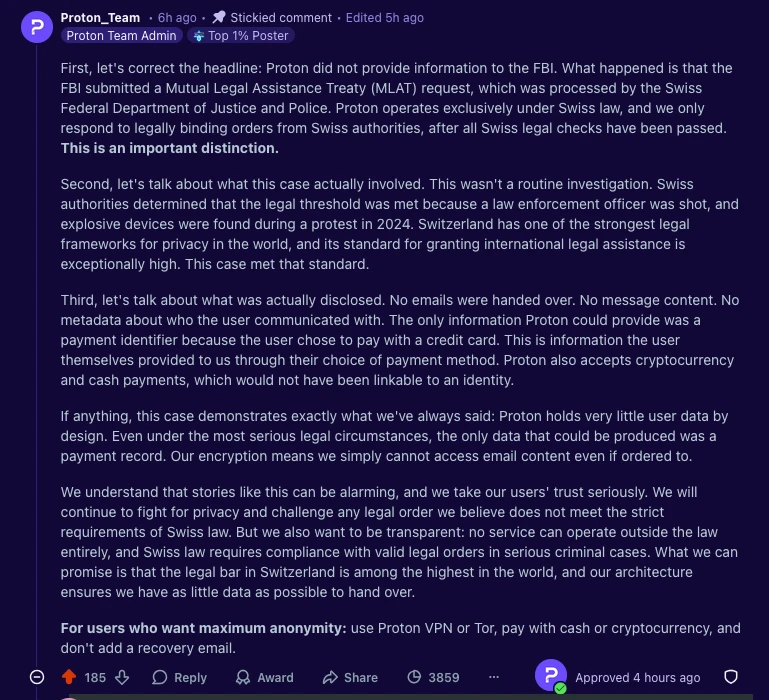
Proton’s defence is correct. Like something a lawyer would write. They minimise retained data, they can’t decrypt message content. None of that contradicts the outcome. They didn’t “help the FBI.” They complied with Swiss law… which helped the FBI. “We only respond to Swiss authorities” is accurate. It’s also doing a second job. Swiss authorities are exactly how foreign requests arrive.
“It is true that Proton is located in Switzerland and responded to a legal request from the Swiss authorities. But it is also true that most people do not know what an MLAT is and there is a widespread misunderstanding that using Proton will protect your account from US govt requests.” — Eva Galprin
Jurisdiction isn’t a magical barrier developed by the Elves around Rivendell. It’s a routing layer. You aren’t choosing whether law applies. You’re choosing which legal process applies first, and under what thresholds it hands off to another one. It’s a friction point. Stick this in your threat model: Navigating tech sovereignty is only going to be harder in this emerging world of backyard hegemonic geopolitics.

Still, we’re not all dodgy billionaires trying to remain afloat in international waters. Sovereignty is the new flavour for us common folk, too. There are plenty of valid reasons to move your stack out of an adversarial jurisdiction. The recent surge in “leave Big Tech” guides makes that clear, from mainstream pieces to a growing number of personal migration logs documenting the process in detail.
- The Guardian — Leave Big Tech behind! How to replace Amazon, Google, X, Meta, Apple – and more
- Coinerella — Made in EU: It was harder than I thought
- Zeitgeist of Bytes — Bye Bye Big Tech: How I Migrated
- Disconnect Blog — Getting off US tech: A guide
These are all good posts for those wanting to migrate their bits. The change they reflect is the impetus. These kinds of guides used to be about switching to open source. Now they’re about geography. The Faustian bargain trade-offs return when you go indy. Missing features. More payment gateways. Interoperability gaps. The quiet reintroduction of complexity that hyperscalers spent decades covering with UI development and SSO paths.
It’s still probably worth it, but what emerges is less of a clean break and more of a negotiated position. It’s partial exits, and hybrid stacks with work-arounds. It looks less like independence and more like jurisdiction curation. If you’re not escaping entirely, at least you’re selecting your dependencies. Maybe that’s enough for the period we’re in. For now. Or maybe not. We’ll find out. These are exciting times.
You can’t unscramble the egg and put it back in its shell. Both national and individual attempts at gaining technological “sovereignty” (or independence, or whatever) run up against the fact that we’ve already made the omelette. Yeah, I’m mixing a lot of metaphors. I’m not un-mixing them. It’s too late. Go with it. Consider torrents, Hollywood, Bollywood, the IIPA, and DNS (you didn’t see that coming).
Christian Dawson, Executive Director of the i2Coalition, recently wrote about anti-piracy enforcement rulings in the Delhi High Court that go beyond holding websites violating copyright laws accountable, or instructing Indian ISPs to block them, and are now green-lighting legal action against domain registrars. The International Intellectual Property Alliance (IIPA) praised the court, Dawson noted, claiming hundreds of piracy sites have already been wiped from the internet as a result. This enthusiasm was share shared by many other U.S. rights holders, who have welcomed India’s approach as a model for tackling piracy globally.
“If you stop there, India’s approach sounds like a win because the temptation is to measure success in takedown numbers” wrote Dawson. “But enforcement architecture matters more than weekly disruption statistics. If the structure being built today erodes jurisdictional limits, proportionality, and procedural safeguards, rights holders may find that the same tools celebrated in one case become destabilizing in many others.”
“Are we prepared for a world in which a single national court can, under its own standards of proportionality, functionally shape global DNS operations through orders directed at infrastructure providers, including foreign companies? Because once that door is open, it does not stay limited to piracy. It never does.” — Christian Dawson
Where’s your sovereignty sit within any of that?
The urge to flee is growing more common. Migrants want to be where it’s safer. Don’t we all? What are they fleeing in this digitised context? No one before the start of 2025 talked about internet sovereignty outside of niche academic circles or the deepest pits of policy wonkery. Now it’s the stuff of blogs and launches hundreds of LinkedIn hot takes on a daily basis. What changed? America did.
Under the Trump administration the DOJ is ignoring the Privacy Protection Act to go after journalists it isn’t happy with. Congress is working across the aisle to abolish anonymous speech on the internet and speed through legal mechanisms that would open the floodgates for unprecedented levels mass surveillance and censorship.
And then there’s just stuff like this I can’t quite categorise, in which people are now looking at how to nip in the bud the worst possible elements of the forthcoming nightmare existence they see coming around the bend…
The [Washington] state Senate unanimously passed legislation Wednesday that prohibits employers from requesting, requiring or encouraging employees to have microchips implanted in their bodies. The bill previously passed the House of Representatives on an 87-6 vote last month. It now heads to the governor’s desk for final approval. — The Seattle times
This is all about fleeing the U.S. Even if you’re not in it, your bits probably are, at least to some degree. “Day by day, the United States is becoming more overt in using its economic and technological influence against its adversaries,” writes Reem Almasri, “which makes the question of independence from dominant US technology companies increasingly urgent.”
“The United States has become the world’s biggest bully, threatening any country that doesn’t do as it demands with tariffs, and its tech companies are taking full advantage by flexing their muscle and trying to avoid effective regulation around the world. The drawbacks of our dependence on US tech companies have become more obvious with every passing year, but now there can hardly be any denying that where we can pry ourselves away from them, we should make the effort to do so.” — Paris Marx
There’s good reason for all this distrust. But the problem is thornier than it might appear. American infrastructure is deeply entangled in the services we use every day. It isn’t always transparent about where it sits. The Dutch government commissioned a legal review of Amazon’s “European Sovereign Cloud” (marketed as sovereignty-friendly) only to quietly pull the report after experts pointed out all the gaping holes and risks. It doesn’t matter where the data centre sits or who staffs it. If the provider is an American company then the U.S. has a long arm of the law to compel access or suspend services entirely.
“The technology is delivered as a black box. To ensure the security of government data, you want to check at the source code level for backdoors.” — Nitesh Bharosa, Professor of Government Technology, Delft University of Technology
The opacity is the problem. Even a government department actively trying to assess the risks couldn’t see inside the product it was evaluating. For individuals, the challenge is even greater. American (and other) cloud infrastructure hides inside apps, services, and platforms in ways that are rarely disclosed and almost impossible to audit.
Writing in Sovereignty for Sale, Sam Freedman argues that this dependency is no longer just a commercial inconvenience. A case in point: Elon Musk’s decision to restrict Ukraine’s use of Starlink terminals showed how control over foreign-owned technology can alter the course of a war. For anyone — individual or nation — relying on infrastructure they don’t control and can’t inspect, the risk is real, even when it’s invisible.
My point — and I do have one — is that we need another way. Signal is a U.S. based platform, but I trust it, for good reasons. Telegram has a global network of servers and is based in Dubai. For good reasons no one should trust it as a secure messenger. I see your jurisdiction, and raise you a security posture, protocol selection or technology architecture that renders it moot.
One size never fits all. This isn’t off-the-rack on the high street. That’s what you were escaping, remember? For file storage, encrypt locally before anything touches a cloud. Your keys, your ciphertext, nobody else’s problem to solve. For email, client-side end-to-end encryption means mathematically unreadable, not “we promise we can’t read it” unreadable. For social, federated protocols like ActivityPub mean your identity isn’t owned by a single company in a single jurisdiction that can be leaned on. For web traffic, encrypted DNS stops queries being snooped at the network level, where a lot of quiet surveillance actually happens. For messaging, the question is how useless that encrypted blob will be when a subpoena lands and metadata was never logged to begin with.
What if it’s building blocks instead of borders? Open protocols offer part of our third path. They invite participation in shaping them rather than simply consuming. They’re transparent instead of uninspecticable intellectual property. And that’s the rub. We’ve been trained by decades of internet concentration and user interface design to see it purely within consumer contexts instead of a series of technical decisions that have consequences, trade-offs and alternatives. You don’t solve all of these things with a re-occurring monthly ding on your credit card. You can’t subscribe your way to safety.
“The sovereignty offered by this approach is not about ownership, but about institutions understanding how their systems work, being able to participate in them, and retaining the option to move or adapt if needed.” — Kelly Roegies
That last part is the key. The goal isn’t to build a bunker. It’s to avoid being trapped. We can’t unmake the omelette. We can only use it as an ingredient to mix into something new. It’s not that your data location isn’t relevant, of course it can be. It’s just that it’s far from the only ingredient that’s relevant.
Sovereignty ≠ Freedom